FAQ Data protection and information security
FAQ Data protection and information security
Data protection is an increasingly important issue. But the security of information in general is also an important concern for the university. However, the subject matter is also quite complex. For this reason, you will find an overview of the most important questions and their answers relating to data protection and information security in relation to typical activities at the University of Oldenburg.
Much is regulated in the General Data Protection Regulation (GDPR). The GDPR is an EU regulation that came into force on 25 May 2018. It contains a number of provisions and requirements for the protection of personal data that must also be observed by the university. You can find out here which provisions of the GDPR must be observed in everyday working life and how you can protect data as well as possible against unauthorised access.
You can find further information at Working in compliance with data protection and IT security in the workplace.

The GDPR in everyday working life
You can find out which general provisions of the GDPR must be taken into account in your day-to-day work, which rights data subjects have and which data must be specially protected here.

Data protection in email correspondence
Email addresses are always personal data, which is why the GDPR must also be observed here. You can find out what you should consider when dealing with emails here.

Social media, Academic Cloud etc.
The use of various apps and services is often questionable in terms of data protection law. You can find out which services you can and cannot use at the university here.

IT security
Nowadays, the protection of sensitive data always includes measures that specifically secure digital data or make unauthorised access more difficult or, at best, prevent it. You can find out what measures you can take here.

Special requirements in research
Research often involves working with personaldata. You can find out what you need to bear in mind when conducting web-based surveys, for example, or what anonymised data is here.

Photos, notices, paper documents
There are other areas in which the rights of others must be protected, e.g. the "right to one's own image", protection of analogue personal data, etc. You can find out how to act in compliance with data protection regulations here.
The GDPR in everyday working life
Who can I contact if I have a question?
Please contact the for:
- Organisational questions regarding data protection
- Questions about the register of processing activities
- Requests for information in accordance with Art. 15 GDPR
- Questions about training programmes
- Notification of violations
Contact the for:
- General questions about data protection
- Confidential enquiries and/or complaints regarding data protection
- Questions about data subject rights
What is the GDPR and who is responsible for compliance with the GDPR?
The abbreviation GDPR stands for a directly applicable European regulation, the "General Data Protection Regulation". Since May 2018, this has primarily regulated what must be observed when processing personal data.
The GDPR has thus largely replaced the BDSG (German Federal Data Protection Act), although the latter still contains supplementary regulations. There are also state laws that provide further supplementary regulations for data protection. For example, the NDSG (Lower Saxony Data Protection Act) and individual provisions of the NHG (Lower Saxony Higher Education Act).
The University of Oldenburg, represented by the President, isresponsible for compliance. In other words, the Presidential Board. However, all employees and students are also bound by the provisions of the GDPR if they process personal data in the course of their work at the University of Oldenburg.
How long can I store the data?
In principle, personal data may only be processed until the purpose of the processing no longer applies or has been achieved. The data must then be deleted.
In the area of research, it is not always possible to determine in advance the exact purposes for which the data can still reasonably be used. Therefore, if a purpose cannot yet be specified in such concrete terms, it is advisable to set a maximum storage period of 10 years. The limit of 10 years represents recognised good academic practice.
In exceptional cases and with appropriate justification, the storage period can of course be set longer.
Please note, however, that the cessation of the purpose should always be the primary deciding factor for the deletion period of personal data.
Information only to authorised persons
Problem:
The controller must ensure that information on the processing of personal data is only provided to persons authorised to receive such information. The identity of the person requesting information must therefore be disclosed.
Solution:
The more sensitive the personal data, the more certain the identity of the requesting person must be. Normally, it is sufficient if the identity appears plausible. Depending on the situation, a distinction must be made as to how the identity should be (plausibly) proven.
- This can be determined in a telephone call by asking appropriate questions. For example, the date of birth, a specific assigned identifier or the student ID number can be asked.
- In a personal conversation, it should be sufficient to ask to see an official photo ID or student ID.
- In the case of written enquiries, the person should have already provided sufficient information about their own data in advance. In other words, they should have already provided relevant and specific data in their letter of motivation so that you can be sure of their identity.
Note:
Only organisational information should be given by telephone. For anything more extensive, it is strongly recommended that you provide this in writing or electronically by email.
What do I need to bear in mind with a declaration of consent?
If the processing of personal data has no other legal basis, or if it is to be based on "two legs", a declaration of consent can be used to create a legal basis.
Obtaining a declaration of consent serves to prove the voluntary nature of the declaration. It must contain sufficient information about the planned data processing so that the data subject can understand what they are consenting to.
Therefore, the declaration of consent must at least include
- Purpose of the processing
- List of the data categories
If necessary, reference can also be made to an existing, corresponding privacy policy. A so-called "media break" is also permissible here.
In the case of electronic declarations, care must be taken to ensure that an opt-out procedure is not permitted. This means that the boxes for ticking must not be pre-ticked when the page or electronic document is called up.
Once consent has been given, it can be revoked at any time.
You can find further information on preparing a declaration of consent here.
Behaviour in the event of a breach of data protection regulations? (Data breach)
If you become aware of a data breach that poses a risk to the rights and freedoms of natural persons, you must report this to the data protection officer. immediately so that they can submit a report to the supervisory authority within 72 hours and inform those affected.
Data transfer to the USA
Data transfer to the USA via the EU-U.S. Data Privacy Framework (adequacy decision)
What has happened?
On 7 October 2023, the European Commission adopted a new adequacy decision for the EU-U.S. Data Privacy Framework (successor to the "Privacy Shield"), certifying an adequate level of protection for certain U.S. companies.
What does this mean?
With the new adequacy decision, it is again possible to legitimise the processing of personal data by U.S. companies without the need for further transfer instruments, such as standard data protection clauses / standard contractual clauses or additional measures, such as encryption.
The basis for the adequacy decision is a decree signed by President Biden ("Executive Order on Enhancing Safeguards for United States Signals Intelligence Activities"). The decree provides the following for Europeans whose personal data is transferred to the USA:
- binding safeguards that limit US intelligence agencies' access to the data to what is necessary and proportionate to protect national security,
- enhanced oversight of the activities of the US intelligence community to ensure compliance with the restrictions applicable to surveillance activities; and
- the establishment of an independent and impartial appellate process, including a new privacy review tribunal, to investigate and resolve complaints about access to data by U.S. national security agencies.
However, this only applies to U.S. companies that have certified themselves in accordance with the Data Privacy Framework. Whether this has been done must be checked in advance.
The adequacy decision is not time-limited, but is continuously reviewed by the European Commission with regard to developments in the USA.
Where can I obtain further information and who can advise me?
Further information on the EU-U.S. Data Privacy Framework can be found here:
https://www.bfdi.bund.de/SharedDocs/Kurzmeldungen/DE/2023/17_Angemessenheitsbeschluss-EU-US-DPF.html
and here: https://ec.europa.eu/commission/presscorner/detail/de/qanda_23_3752
The Data Protection and Information Security Unit will be happy to advise you on the admissibility of data transfers to the USA or other third countries. The best way to contact us is by email at :
Can I read about this somewhere?
Further information on the topics of data protection and information security can be found at Working in compliance with data protection and IT security in the workplace.
For members and affiliates of the university, a comprehensive script on data protection law is available, which you can download here [on the intranet] as a PDF document along with other interesting documents on the subject of data protection:
Data protection in email traffic
Business and student use of Microsoft Outlook apps
Microsoft has released a new, free Outlook app for Windows 10 and 11 in addition to the classic Outlook application. This free application synchronises access data, including passwords, and emails with the Microsoft cloud. For this reason, the app may not be used for work purposes at the University of Oldenburg for information security and data protection reasons. Students are not permitted to use the app to access university email addresses. The same applies to the Outlook apps on mobile devices (Android and iOS) and Outlook 2021 on MacOS. For mobile access to emails, we recommend using the webmail function: https://webmail.uol.de or https://w.uol.de for short. This expressly does not apply to the classic Outlook application from the Microsoft Office package (Office 2016, Office 2019). You can find instructions on how to use webmail at IT services: https://uol.de/itdienste/services/groupware/outlook-web
Avoid phishing
Phishing originally referred to fishing for passwords. Nowadays, however, it usually refers to emails that are intended to deceive the reader in order to obtain confidential data.
The first version pretends to be from a known sender and aims to trick the reader into clicking on the link it contains. This link does not lead to a known website as claimed, but to a fake. If the user enters their password to log in, the attackers have achieved their goal.
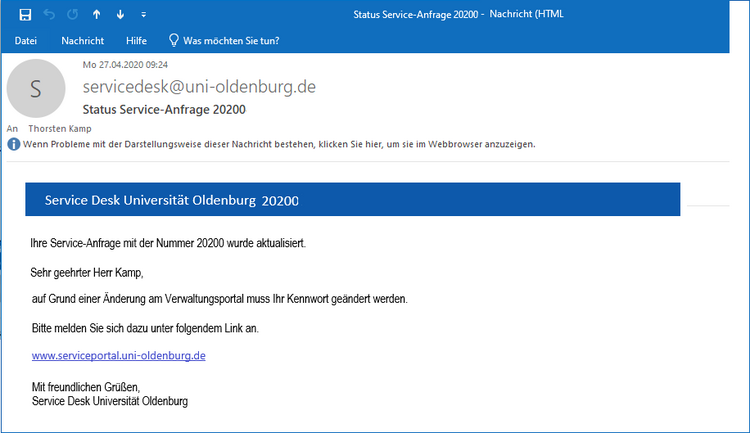
In the second version, a file is sent as an attachment for the recipient to open. This file then contains a virus.
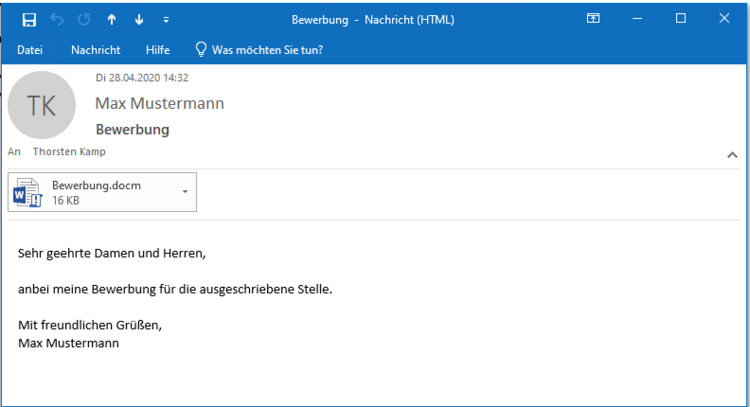
Recommendation
When you receive an email, check whether the content is plausible. Have you already had contact with the sender on the subject? Are you expecting the message or this reply? Has the sender actually promised to send you a file?
Viruses often intervene in an existing conversation and send a supposed reply in connection with a virus file.
Would the sender write to this email address?
Your bank will probably not send an email to your University of Oldenburg email address.
If an email unexpectedly asks you to log in to a website, never click on the link. Open a web browser and type in the known address yourself.
Tip: If you move the mouse pointer over a link in your email without clicking on it, you can see where the link actually leads to.

Be suspicious of files in emails. If you receive the file unexpectedly, do not open it.
And if you receive a security warning that macros are deactivated, please do not activate the virus.
![]()
By the way: If you receive suspicious emails, you are welcome to forward them to !
Dealing with email addresses
Problem:
Email addresses are always personal data. Even if the email does not contain the first name and surname of the person concerned.
Therefore, a legal basis is always required to process email addresses within the meaning of the GDPR, i.e. to store them, send content to an email, etc.
Solution:
If you want to collect email addresses from publicly disclosed websites yourself:
Differentiate where the email data comes from.
First of all, it is important to determine whether the respective institution/office/organisation and the respective recipients are likely to have at least an imputable interest in the content of the email to be sent.
Furthermore, the potential recipients must also have at least presumably publicised their email in such a way that it can be expected that they will also be contacted regarding the respective content via this email and also have an interest in this.
If this is not the case, you need a legal basis for the processing of personal data (= here: storing and sending emails from and to "third parties" of the respective institutions). This can normally only be achieved with consent. However, you do not usually have this.
If you want to access an email address list of another institution/agency/organisation:
Clarify with the respective institution/agency/organisation whether they are allowed to pass on corresponding email address lists to you. This is usually only the case if the employees and relatives have already given their consent for their data to be passed on to third parties for the purpose of the respective content. Concrete purposes here are likely to be regular: Information offers, invitations to specialist conferences, participation in research studies, etc.
If the employees and relatives have not given their consent, you would have to ask the respective institution/body/organisation to obtain the consent of the potential recipients.
Handling the TYPO3 Powermail form
Problem:
If you use the Powermail form function on your website, you save the content entered by the users of this form and their specified email address by default.
As soon as the form has been completed and sent by the user, you can view the completed input options via the "Powermail" tab on the one hand and the "List" tab on the other. The last entries are also displayed in the content element that you use to display the Powermail form on your website. The data is therefore "processed" here in accordance with the GDPR.
Solution:
Maintain the stored data regularly: Delete the content when it is no longer needed. Export the email addresses regularly if you have only set up Powermail for this purpose (e.g. for distribution lists or newsletters) and then delete the content in Typo3. You can do this either via the "Powermail" tab or via the "List" tab.
Data protection notice for contact forms, newsletters & email distribution lists
Problem:
When setting up newsletters and email distribution lists via the websites of the University of Oldenburg, there are information obligations under Article 13 GDPR. Among other things, the purpose, legal basis, duration and type of data processing and, in particular, the type of categories of personal data and much more must be stated.
Solution:
In simple cases, it is sufficient to refer to the university's privacy policy. This is the case, for example, with simple contact forms, newsletters & email distribution lists.
However, if more data is requested than is covered by the university's privacy policy, you should create your own privacy policy. If you would like advice on this, please contact the Data Protection and Information Security Unit at
Open email distribution list
Problem:
Data protection requirements must also be taken into account when designing email distribution lists, as (at least personalised) email addresses are personal data within the meaning of the GDPR.
If an email distribution list is used in which all recipients are addressed in the "TO" or "CC" field, the recipients are visible to all other people in the distribution list. The content of the email can be used to obtain additional information about the group of addressees beyond the mere email address (e.g. if all addressees are graduates of a particular degree programme). In terms of data protection law, this is then a "transmission" to third parties, which is only permitted on the basis of a legal provision or the consent of the data subjects.
Solution:
Instead of the "AN field" or "CC field", email addresses should be entered in the "BCC field" (blind carbon copy). This makes it impossible for the addressee to recognise to whom else an email has been sent.
Your own email address is entered in the "TO field". This means that you send the email to yourself, but the recipients you have entered in the BCC field will still receive the email.
"Unsubscribe" function
You should also create and communicate with every email the option for recipients to unsubscribe from the mailing list at any time. This must be just as easy to do as it was to subscribe, i.e. regularly by a simple reply email or by clicking on an "Unsubscribe" button. The data subject must have the option of no longer receiving emails and being removed from the mailing list.
Note:
This does not apply to "setting in CC" as part of the fulfilment of official tasks in (internal) email correspondence. However, restrictive handling is also recommended here.
Social media, Academic Cloud etc.
Use of the Academic Cloud
University members are generally entitled to use Academic Cloud services insofar as this is necessary to fulfill their official duties. The University of Oldenburg has concluded corresponding contracts with the provider, Gesellschaft für wissenschaftliche Datenverarbeitung mbH Göttingen (GWDG).
Registration, GWDG terms of use and data protection information
- General use:
In principle, you may use all services available under Academic Cloud Services subject to the following scope of use (see Section II).- Exception: The "ActionBound" tool is not permitted for business use.
- Registration:
Registration takes place via the website https://academiccloud.de.- Please select "Federated registration" and log in by selecting "Carl von Ossietzky University Oldenburg".
- Terms of use:
- The terms of use of the GWDG apply.
- Individual services may contain additional, service-related terms of use, which must also be observed.
- Data protection information:
The GWDG provides data protection information that contains all relevant information on the processing of personal data. This is available at https://academiccloud.de/privacy/.
University terms of use and contractual restrictions on use
1. Principle of use
- When using the Academic Cloud, take care to protect your own personal data as well as that of others.
- The Academic Cloud is primarily intended for cross-university collaboration. It should only be used if your task cannot be accomplished with the tools provided by the University of Oldenburg (e.g. Big Blue Button, UOL-Cloud, Stud.IP) or only to a much lesser extent.
- Particularly in the area of administrative tasks, personal data must be anonymized wherever possible before it is stored in the Academic Cloud.
2. Permitted use of the Academic Cloud
Personal data may only be processed in the Academic Cloud if:
- this is absolutely necessary for the fulfillment of the task and
- prior anonymization is not possible.
Examples of personal data
- name: Always personal, as it refers directly to a specific person.
- telephone number: Personal if it can be assigned to a specific person.
- e-mail address: Personal if it refers to a specific person.
- personnel or student number: Personal, as it is clearly assigned to a person.
- gender: Usually not unique on its own, but becomes personal in combination with other data.
- profession: Personal, especially in a specific context (e.g. "President of a university in Oldenburg").
- audio recordings: Personal, unless the voice has been irretrievably distorted.
- image and video data: Personal if faces or other individual characteristics (e.g. tattoos) are recognizable.
Permitted data categories in the Academic Cloud
Only the following data categories may be processed in the Academic Cloud under the conditions above and below:
- audio recordings
- authorizations/profiles
- image recordings
- budget
- contact data
- passwords
- pseudonyms
- master data
- connection and usage data
3. Unauthorized use of the Academic Cloud
The processing of the following data in the Academic Cloud is prohibited:
- Specially protected data in accordance with Article 9 GDPR:
These categories of data are particularly sensitive and are subject to strict protection. These include:- data on "racial" [sic! GDPR wording] and ethnic origin
- political opinions
- religious or philosophical beliefs
- trade union membership
- genetic data
- biometric data for the unique identification of a person (e.g. fingerprints, facial recognition)
- health data (e.g. diagnoses, medical history)
- data on sexual life or sexual orientation
- Official and business secrets of the University of Oldenburg
- Non-disclosure agreements: Content that the University of Oldenburg is contractually obliged to keep confidential.
- Data from the performance of official duties:
- personal or case-related data that arise in the context of self-administration tasks of a sovereign nature.
Translations using EU Language Tools (e.g. eTranslation)
Problem:
When using external translation or AI services, there are often uncertainties in terms of data protection law. It is often unclear which data is transmitted to the provider, whether the data is used for commercial purposes or for training AI models, whether processing takes place outside the EU and whether logging makes it possible to monitor the performance or behaviour of employees. With commercial translation or cloud services in particular, there is a risk that entered texts will be permanently stored, analysed or passed on to third parties.
Solution:
The university uses the EU Language Tools language-tools.ec.europa.eu provided by the European Commission for translation purposes (e.g.
eTranslation). The services are accessed via the access management system provided by the European Commission (EU Login). These services are considered suitable under data protection law because
- the European Commission operates the services under its own responsibility,
- the processing takes place exclusively within the European Union
- the texts entered are not used for commercial purposes,
- the data is not used to train the AI models,
- the texts are only processed temporarily and are not stored permanently,
- the systems are subject to high technical and organisational security requirements.
Use of the EU Language Tools is voluntary. There is no obligation to use them. In case of uncertainty regarding the protection of the content, alternative
translation channels can be selected.
What content may be translated using the EU Language Tools?
In particular, the following are permitted
- Website and publicity content
- General administrative and information texts
- Study information without reference to individual persons
- Texts that contain personal data in passing at most
In particular, the following are not permitted
- Personalised special categories of personal data (e.g. health data)
- Personalised examination and performance data
- Personalised personnel files and application documents
- Confidential research data
- Minutes from confidential committee meetings
- Legal and conflict documents
Handling data via cloud services, messenger services or groupware services (e.g. Skype, WhatsApp, Dropbox, OneDrive, Facebook, Skype, Gmail)
Problem:
The use of external cloud services (e.g. Dropbox, OneDrive), messenger services (e.g. WhatsApp) or groupware services (e.g. gmail, icloud) is often very questionable in terms of data protection law. This is due to the fact that it is often not clear at first glance which data is transmitted when using such services and which of it is encrypted or whether the providers are subject to or comply with the data protection regulations applicable in the EU.
The fact that metadata can be stored and forwarded when using messenger services such as WhatsApp and Threema is a particular cause for concern. In addition, both services may allow access to the user's contact list, which would give the services access to other people's phone numbers. Another complicating factor with Skype is that video calls are generally not encrypted.
Solution:
Only data protection-compliant cloud, messenger and groupware services should therefore be used. These include:
- NextCloud (via the university website)
- DFNconf (web and video conference with multiple participants)
Secure handling of files in the cloud
Problem:
With the various options for file sharing in the university cloud (https://cs.uol.de), it can quickly happen that unauthorized persons gain access to the data by mistake or out of ignorance.
Solution:
Before sharing files, think carefully about who should have access to the files. You have the following options for controlling sharing:
- Internal sharing
If possible, always use the "share directly with members of the University of Oldenburg" option when sharing files that are not intended for the public. This requires the recipients to log into their user account before they can access the file. This increases security and protects our data. - Public links
In exceptional cases, it may be necessary to create public links. However, these must be password-protected. Make sure that the password
- is not easy to guess,
- is provided via a second communication channel (e.g. separate e-mail or telephone). - Limit or revoke access rights
If possible, only grant access rights for a limited period of time. If this is not possible, regularly check the assigned access rights and shared links and revoke them as soon as access is no longer required. This helps to prevent unauthorized access to our data. - Keep an eye on data protection
Always be aware of what information you share. Avoid sharing confidential or sensitive data via public links. Your sense of responsibility is crucial to protect our data and minimize security risks.
Information on the cloud
The IT services provide a brief description and instructions on how to set up your personal cloud.
Contact
If you have any technical questions or uncertainties, please contact our IT services at any time. For data protection and information security queries, please contact the DISM staff unit.
Use of social media accounts for an Institute
Problem:
The ECJ has ruled that operators of a Facebook "fan page" are acting in a so-called "joint controllership" with Facebook Ireland for the processing of personal data. (ECJ ruling of 5 June 2018, case reference: C-210/16). However, as the "fan page" operator has no access to the data processed by Facebook, it is unclear how it should exercise data subject rights. An agreement pursuant to Art. 26 GDPR would therefore have to be concluded between the operator of a "fan page" and Facebook, in which in particular the exercise of data subject rights is regulated. However, Facebook does not currently offer such an agreement.
In addition, when implementing the "Like" button on your own website, (personal) data of a user is transferred to Facebook (even if this user is not logged in to Facebook).
Solution:
Avoid sending data to Facebook by not implementing the "Like" button on your website or contact the university's regarding a data protection-compliant implementation ("two-click solution"). This also applies to the implementation of other social media services (e.g. YouTube, Twitter etc.) on university websites.
In addition, the social media services used by the university should at least include a suitable link to the university's privacy policy.
If you have any questions about the official use of social media services, please contact the .
Use of "Doodle" to coordinate appointments
Problem:
When making appointments via Doodle, you not only provide Doodle AG, a company based in Switzerland, with your email address and name, but also, if applicable, the business reason for the appointment. This may violate both the employer's confidentiality interests and data protection concerns. This is because the fact of whether and with whom you communicate on business is also subject to confidentiality.
Doodle also uses Google Analytics and other analysis mechanisms that enable profiling and targeted advertising.
Solution:
Appointments can also be conveniently coordinated via Microsoft Outlook, which is installed on all work computers. The data then generally remains within the university network.
Should it nevertheless be necessary to use an external service, the more data protection-friendly alternative offered by the DFN (German Research Network) at terminplaner.dfn.de should be used. Here, data transmission is encrypted, the survey can be set with a deletion date and the activities are neither analysed nor do you receive advertising.
Why does the university currently not allow tools from external providers (such as Microsoft Teams, Skype, Zoom, etc.) for digital communication?
The University management is legally responsible for protecting the personal data of its members and affiliates (and guests, if applicable), takes this responsibility very seriously and therefore prioritises the tried-and-tested DFN-Verein (German Research Network) tool, which is optimally integrated into the University's digital infrastructure, and, as a supplement in the current situation (performance difficulties at DFN), the self-hosted (operated) tools for digital communication set up by the University's IT services at short notice (see uol.de/itdienste).
On the one hand, these have the advantage that they can be "controlled" by the university itself and the (personal) data traffic does not run via third-party systems/servers, which may be contractually obliged to comply with local data protection standards (in particular those of the European General Data Protection Regulation; GDPR), but may also be subject to divergent laws of the countries in which the companies are based (e.g. the USA). On the other hand, they are integrated into the existing university systems UniCloud and Stud.IP and thus enable easy usability and, in particular, technically uncomplicated (subsequent) use of created digital content (e.g. events, seminars).
The release of third-party systems with which personal data that lies within the university's area of responsibility (can) be processed also requires a careful process of technical and (data protection) legal review, coordination with the Staff Council, the corresponding documentation required by the GDPR and the conclusion of necessary contracts and, as a rule, appropriate licensing.
In addition to the protection of personal data, the protection objectives (confidentiality, availability and integrity) of information security (especially in the case of confidential exchanges/conversations) also play a significant role here.
Many external services do not adequately fulfil the above requirements.
In addition, the university management attaches great importance to a structured approach to mobile communication. This is the only way to avoid "uncontrolled growth" in the use of communication tools and to gain valuable insights for the university's digitalisation strategy as a whole.
However, constructive and specific feedback from all users regarding the current offering is essential for this (and for planning the next steps).
Please send this to the known e-mail address:
Further contacts:
If you have any questions about data protection and information security, you can also contact the Data Protection and Information Security Unit and (especially for confidential matters) the Data Protection Officer.
No use of Google Analytics on UOL websites
Problem:
Google Analytics cannot be used in compliance with data protection regulations for the following reasons:
- Missing but required user consent when accessing the website (this is difficult to obtain in compliance with data protection regulations).
- Invasion of privacy: Google Analytics collects a large amount of personal data from website visitors, including IP address(es), surfing behaviour or demographic data.
- Limited transparency: Google Analytics works like a black box and offers only limited transparency regarding its data collection methods and algorithms.
- Ownership of the data: Ownership of the data is essentially ceded to Google.
Solution:
Matomo (formerly Piwik): An open source web analytics platform that allows you to host the data on your own servers, giving you full control over your data and ensuring data protection. It is already in use at the UOL. If you have any questions, please contact .
IT security
IT security in the workplace
IT security at the University of Oldenburg depends on each individual employee. We have therefore compiled information on the most important security risks in the workplace and how you can minimise them separately for you here.
Can I save passwords in the browser?
No. Storage is insecure and passwords can be stolen. It is better to use a password safe.
How can I save passwords?
There are so-called password safes for storing passwords. These are programmes that save the stored passwords in an encrypted, password-protected file. Instead of, for example, 30 passwords, you only have to remember a single password, the master password. Consider whether you want to use a different, longer password as the master password than for your university access. And don't share this master password with anyone.
The best-known password safes include the Keepass programme(keepass.info/) and its offshoot KeepassXC(keepassxc.org/).
You can also use these programmes at the University of Oldenburg to manage your passwords. Just make sure that you choose a secure, sufficiently long password for the programme. This is the only password you will need to remember. You save all other passwords in the programme and can copy them and use them to log in if necessary. The programmes also offer a password generator to create secure passwords.
The programmes mentioned are all open source and can be used free of charge.
Special requirements in research
Use of web-based surveys (e.g. for studies)
Problem:
Web-based tools regularly process personal data (such as the IP address or the name of the person). Especially with free text response options, there is a high risk that personal data will be processed.
Solution:
The questions should initially be asked in such a way that no personal reference can be established if they are not interested in the identity of the participants. It should also be noted that no personal reference can be established even when the data is combined. This can be the case in particular with questions about the job title in connection with the question about the respective institution.
Avoid free text options. If a free text option is necessary in order not to conflict with the purpose of the survey, point out to the participants that specific personal data such as names, addresses, telephone numbers, workplaces, etc. should be avoided.
If a third party acts as a service provider for the survey, ensure that they do not have access to the personal data.
- It is best to use tools that are already provided to you by the Data Centre.
- Make sure that you collect as little personal data as possible if you do not absolutely need it
- State the purpose of the survey
- Have the respondents consent to the survey before it begins
- Set completion dates (end and evaluation of the survey)
- Anonymise the data as soon as possible after the survey
- Allow the answers to be corrected (e.g. by logging in later before the end of the survey period)
- Create a register of processing activities and send it to the Data Protection and Information Security Unit
What is the difference between anonymisation and pseudonymisation?
Anonymised data is not subject to the provisions of the GDPR. In principle, it can be processed freely without the consent of a person or a specific legal basis.
Contrary to what the word might suggest, anonymisation does not occur when names are no longer mentioned. Rather, according to the legislator's idea, anonymised data should not contain any personal references .
The data ispseudonymised if it can no longer be assigned to a specific person without additional information. This can be achieved in particular by replacing the name of the data subject with an identifier.
Aggregated data is data in which data from different persons has been merged to create a "data group". These can also no longer be traced back to a specific person, but are therefore not necessarily anonymised.
What is order processing?
If data is not processed by the controller itself, but by utilising the services of third parties, this is referred to as commissioned processing.
For this purpose, a separate agreement must be concluded between the controller as the client and the third party as the contractor (processor).
You can find more information on this here.
Register of processing activities
Problem:
Insufficient documentation of data processing procedures means that, on the one hand, it cannot be proven that only the data that is necessary for the fulfilment of the respective task is processed and may therefore also be processed. In addition, there is a risk that technical and organisational data protection measures are not sufficiently binding and are therefore changed without prior review.
Solution:
For each procedure in which personal data is processed automatically, a procedure description must be created in accordance with Art. 30 GDPR, made available to the data protection officer and kept up to date. The staff unit will assist you with the preparation.
Photos, notices, paper documents
Taking and publication of photos of employees
Problem:
Photos of colleagues are taken time and time again. Whether it's a portrait photo for the company website or a group photo to present your own employees, during a meeting or at a party. Such photos are often published on the company website, i.e. on the Internet, which is generally accessible worldwide.
If the person or persons depicted in the photo have not given their consent, the taking and publication of such photos is unlawful. The persons concerned then have a right to have these photos deleted. However, the persons concerned often do not even know that a photo of them has been taken and published (especially at parties, where photos are often taken out of the situation in order to achieve a high degree of authenticity).
Solution:
Before you take any photos of colleagues, ask them in advance whether they agree to this. If you intend to ultimately publish the photos on the company website (also applies to internal organisation drives) - whether publicly or only accessible to certain people - also ask whether all colleagues pictured agree to this.
Avoid taking and, in particular, publishing photos of the situation if you have not obtained consent to do so.
Consent does not necessarily have to be given in writing, but this can be useful in the event of a dispute (a simple email is also sufficient).
Taking (and publication of) photos at events
Problem:
You are planning a university event at which photos are to be taken for public relations purposes (publication of photos on the university website, etc.) and are wondering how to handle this in compliance with data protection regulations?
Solution:
If you send out invitations, point out on them that photos will be taken for public relations purposes as part of the event and that these will be published (and, above all, where). The notice should also state that you should contact the photographer if you do not wish to be photographed. Contact details for further questions should also be provided. Such a notice should also be placed (if necessary additionally) on a web-based registration form. In addition, clearly visible notices of the above-mentioned type (ideally with a "camera" pictogram) should be displayed outside the premises where the event is taking place.
If portrait recordings (e.g. for interviews) are to be made during the event, please obtain consent from the persons concerned (as well as for publication). This does not necessarily have to be in writing. However, something "in writing" can be useful for documentation purposes in the event of a dispute. You can use the attached sample for written consent.
Notices with personal data
Problem:
The public posting or public display of lists or examinations with student ID numbers and student names constitutes an unlawful transfer of personal data. This is because it is possible to recognise which person has attended which course under which student ID number, taken which examination and, if applicable, passed it with which grade.
Solution:
If an electronic version of the notice, which is only accessible to the person concerned, is not possible, especially when displaying examination results with marking (e.g. in Stud.IP), the analogue notice should only be posted using the student ID number. However, this should only be done to the extent that the student ID number can only be assigned to the person behind it by authorised persons. The assignment of the student ID number to the person behind it must therefore not have been made public.
Conversely, lists of participants should only contain names and not (also) the student ID number.
Disposal of paper documents
Problem:
In everyday office life, many paper documents with confidential content accumulate (e.g. drafts of letters that are not kept on file, misprints of emails, etc.). Disposal via the office wastepaper basket does not ensure that third parties cannot gain unauthorised knowledge of the content.
Solution:
Paper documents with confidential content must be disposed of via the paper collection containers provided by Division 4 (more details here). Disposal on your own is only permitted if a document shredder in accordance with DIN 66399 (security level 3 or higher) is used that is suitable for the protection requirements of the documents.
