ICBM-IT
Please always send enquiries to ICBM-IT via email to
- these will only be read by the team members named on the left.
Latest news from ICBM-IT
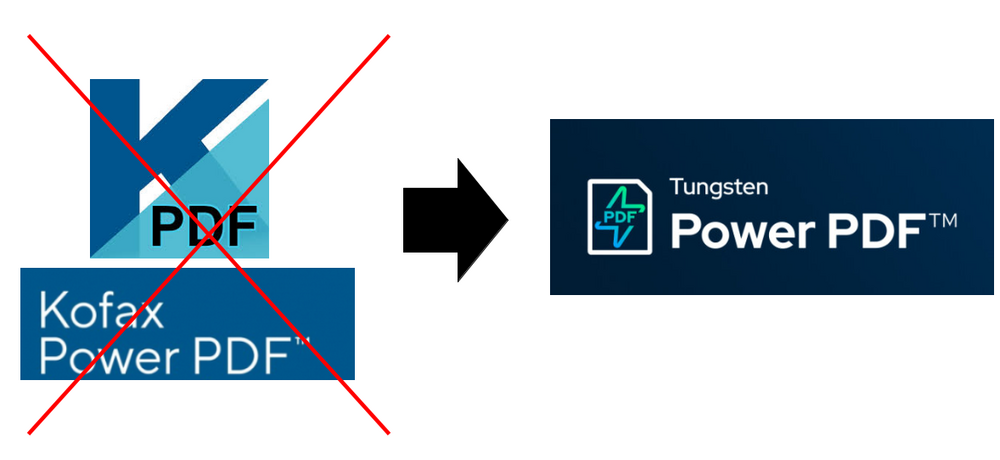
Windows 11: Updated version „Power PDF” (Kofax → Tungsten)
The recent and the upcoming days will see the rollout of a new version of our PDF tool on all Windows 11 clients. The obsolete „KOFAX Power PDF Advanced” will be renamed to "TUNGSTEN Power PDF Business“. Apart from that, all functionalities will remain the same.
Work smartphones and tablets
The department has established guidelines for compliance with data protection and IT security regulations, which are described on the following page:
https://uol.de/en/itdienste/services/business-mobile-devices_intranet
We kindly ask you to take note of this.
Best regards from ICBM-IT
Mission statement
We are service-oriented contacts for all questions and problems in the area of IT infrastructure. We see our central tasks in
- advising on the purchase of IT hardware and the use of central IT services at the university,
- setting up and maintaining an operational software environment,
- monitoring and analysing the IT infrastructure in order to avoid problems in advance and ensure security, and
- providing support for IT solutions to questions of scientific computing and data management as well as online teaching and presentation technology.
Our goals are good communication and transparency as well as sustainable solutions and security.
How do I get support?
Please always send your request by email to (ticket system). You will receive an email reply as soon as possible from the IT team member who has dealt with your request. To prioritise requests that arrive at the same time, please describe the importance and urgency of your request in your request.
Be aware of phishing mails
Just some Links:
- BSI Phishing erkennen
- Phishing im Netz erkennen und vorbeugen
- UOL- DSM FAQ
- Verbraucherzentrale Phishing erkekennen
Und doch noch mal ein eigener Text:
Due to recent incidents we would like to remind you how to take care of spam and phishing mails.
Since even in hacker circles there is a shortage of skilled workers, most spam/fraud is not too intelligent (=dangerous), but thanks to DeepL and ChatGPT at least it looks not that bad anymore. That means it's getting more difficult to detect, On the other hand: looking at the mail is usually still without danger and most of the time clicking on links is not harmful either. Entering anything on the linked pages is FATAL in case of a phishing site.
There are a few basic rules you should follow within EVERY mail:
No matter where the mail comes from and in which program you look at it: BEFORE you click on any link, look in the mails header for the full sender (if you can see it) but that's just a first clue. After that, look at the exact link you want to click on. To do so hover your mouse over the link and the real destination should usually be displayed in the lower left corner (on cell phones, usually long-click the link). After you have clicked on a link, look at the top of the browser address page to see if this is really the institution you want to go to. A few examples to try out:
ICBM IT
ICBM IT
„https://uni-oldenburg.de∕.si42.de/icbm”
None of these links directs to an ICBM or other university page! Last one has to be copied by hand, but obviously it is 'uni-oldenburg.de' between the first slashes after https ;)
This practice of checking links BEFORE and AFTER clicking also applies to clicking links in web pages.
How do I set up a Teams account?
- Instructions for setting up MS Teams (as part of Office365) at university account level can be found at: Register Microsoft account for Teams ...
Which Office version do I have on my computer?
Under Windows, the easiest way to find this out is from within an Office programme. Select the File tab and then Account at the bottom left. Then under 'Product Information' you will see something like `Microsoft Office LTSC ... 2024` - then it is Office 2024, so it should look something like this:
 At (1) you will find the version, the mention of 365 at (2) is just to confuse the uninformed.
At (1) you will find the version, the mention of 365 at (2) is just to confuse the uninformed.
On the Mac, it's a little easier: in an application, click on the menu item with the programme name (e.g. 'Word') and then on the first item 'About Microsoft Word'. There, under Licence: the version also appears as 'Microsoft Office LTSC ... 2024'.

![[Translate to English:]](/f/5/_processed_/3/2/csm_ICBM-Logo-transparent-_91fe1c6774.png)
